Top Pitfalls of the Internal IT Team (and How to Avoid Them)
To handle the deluge of daily tasks, your internal IT team needs to run like a well-oiled machine. From managing security and ticket flow to conducting routine maintenance and proactive monitoring, your team requires expert efficiency to stay at the top of their game.
But all too often, common pitfalls can complicate your to-do list, creating extra work for your team. Recognizing these time traps is the first step to avoiding them—the second step is developing a fool-proof plan to avoid them in the future.
Pitfall #1: Windows 10 and the Perils of Patching
Consider this: When a new patch is released, hackers immediately swoop in to compare the update to the preexisting operating system. This helps them identify where the security loophole is—then use the information to exploit end users and corporations that are slow to patch the breach. In 2018, attackers exploited patch updates to steal valuable personal data on users and payment information. While these instances only account for 6% of the year’s total breaches, the negative consequences for those attacked are profound.
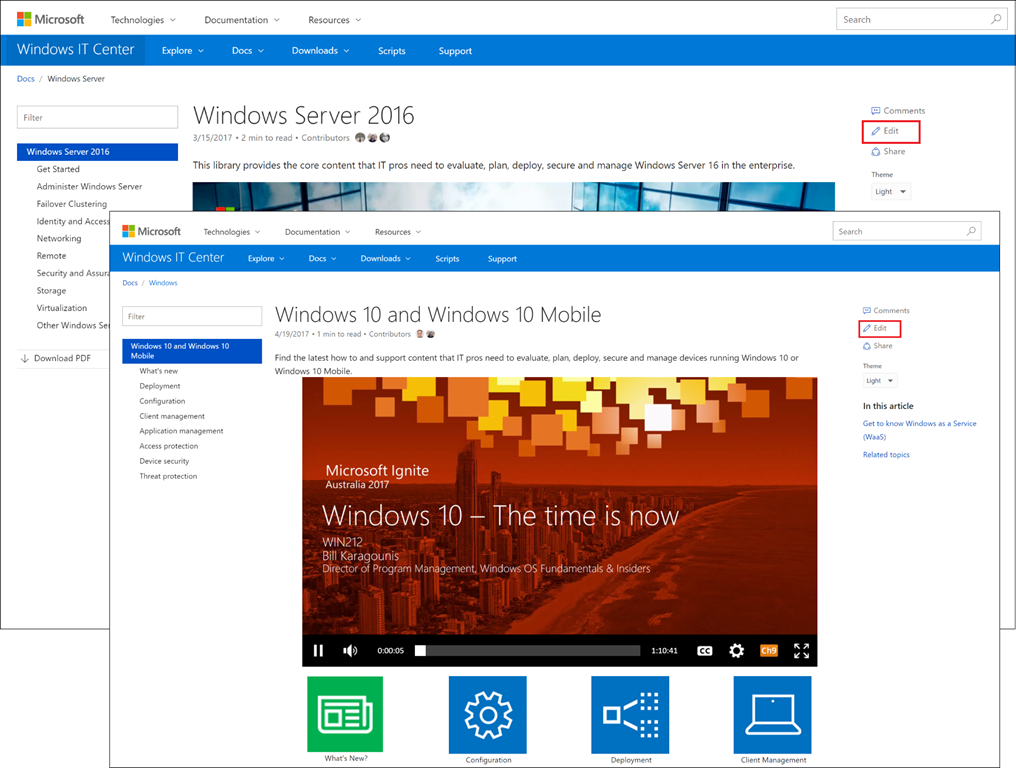
For years, Patch Tuesday helped IT teams keep track of the Microsoft® software updates. But with Windows 10, system fixes are no longer released on such a predictable schedule. That doesn’t mean patching stops being a top priority though. Managing patching is essential to safeguarding your software and machines against external threats.
The best way to avoid this common pitfall is to standardize your team’s policy for automatic Windows 10 patching. Set up alerts to update your team as soon as a patch is released—and enable broad discovery capabilities that cover your company’s entire inventory of production systems. Remember: It only takes one vulnerable computer to put your entire network at risk.
Pitfall #2: Incorrect Ticket Routing
Your internal IT team may field countless help desk tickets a day, and to maintain your high level of customer service, the pressure is on to correctly route each ticket to an expert technician. But with manual routing, there are endless opportunities for mistakes. What’s more, if your team isn’t routing tickets based on knowledgeable resources, you’re creating delays that can throw off the entire routing process—which is bad for business.
To avoid the obstacles that come with ticket routing, consider ditching manual in favor of an automatic ticket routing program. Workflow automation is quickly becoming an industry standard. As more IT teams make the switch, it’s becoming increasingly important that you do the same.
Pitfall #3: The Flaws of Manual Processes
Try as you may, human error is impossible to avoid. And in a complex IT environment, manual processes create the potential for errors that can put your entire workflow—and your system’s security—at risk.
What if a real emergency hits and your team needs to respond quickly? In this instance, the small, day-to-day IT tasks should be set aside in order to deal with the bigger problem. But if these tasks still follow a manual process, forgetting them is out of the question.
The best way to avoid this scenario is by nixing manual processes in favor of automation, whenever possible. For cases where manual is still essential, make sure the process is formalized—and that your team is fully trained to follow protocol.
Pitfall #4: Maintaining an Inventory of Assets
It’s up to you to keep your team’s project on track—but when information is owned by multiple managers and dispersed across countless spreadsheets and documents, project management can be next to impossible. And the more complex the project, the larger your inventory of assets. Talk about an organizational pitfall.
To avoid asset chaos, you need to find a solution that allows key documents, data, and configurations to be readily available to the team members that need it most. This will cut down on the time you spend pinging John for that report or chasing down Sarah for that serial number.
There are a number of solutions that allow for easy asset inventories. Many companies opt for free options, like Google Drive, to cut down on costs. But in doing so, you often lose out on optimal information security. More advanced options at a price are designed to expertly guard and intuitively aggregate assets—meaning everything is kept organized and safe.
Pitfall #5: Repetitive Admin Tasks
There are some things in life we, unfortunately, can’t avoid. Admin tasks often fall into that category. But these day-to-day to-do items, like tracking time, aren’t just tedious—they take valuable time away from other, more vital tasks. When this happens, either the admin tasks aren’t completed, or the more important responsibilities aren’t completed up to par—a no-win situation.
Ask yourself a question: Is your time really best spent making sure your techs are entering their time or tracking down that rogue endpoint? No, probably not. In lieu of hiring a full-time administrative assistant, try using a program that can consistently complete admin tasks. This way, you can focus your attention on bigger, more important projects while the tedious—but necessary—tasks get done.
Pitfall #6: More Reactive Than Proactive
As an expert IT professional, you can spend a lot of time putting out fires. System bugs, holes in security—whatever the issue, once you fall into the habit of taking a reactive approach to problems, you’re already losing efficiency. And when you’re inefficient, the end users’ productivity is plummeting.
A proactive approach to solving internal infrastructure issues is far superior, allowing you to fix infrastructure issues before they happen. The right software can help make this process that much easier; but before choosing one, consider these two key components of proactive IT problem-solving.
First, you need the ability to easily monitor and remotely control sessions. This will give you valuable insight into your team’s workflow and efficiency. Second, search for a program that facilitates system response monitoring. This will help improve your overall response time, so you’ll spend less time putting fires out. Renewed speed will also impress your end users, earning your team a reputation for efficiency.
With the right product and processes in place, your team will gain a firmer grip on proactive operations—and be more prepared to tackle reactive situations.
This article was provided by our service partner Connectwise.com