How Threats Have Evolved & Why You Need to Do Something About It
Whether you realize it or not, the
cybersecurity threat landscape has changed dramatically in the last few years—and recent security issues prove it.
Everywhere you turn, conversations about cyber issues today are happening. The media coverage on massive breaches continues to grow by the day. But since most of the high profile cases people read about are large companies (Equifax, Apple, Target, etc.), many small business owners you work with have it in their mind that large companies are the targets and they’re immune or safe from new threats.
That couldn’t be further from the truth.
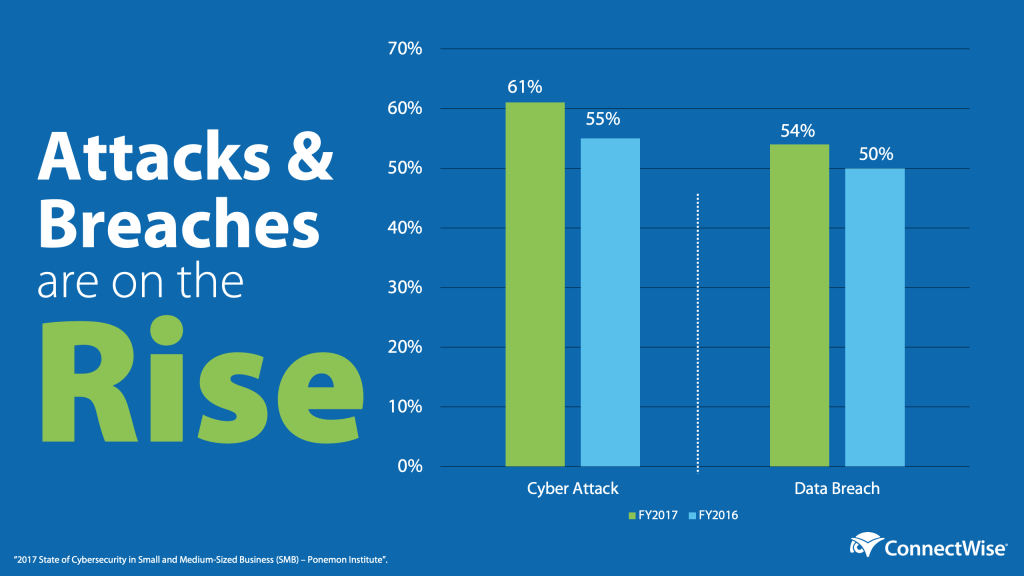
Attacks on SMBs, as well as MSPs, are on the rise, and you both must be vigilant as a result. According to the Ponemon Institute: 2017 State of Cybersecurity in Small & Medium-Sized Businesses (SMB) study, the average cost due to damage or theft of IT assets and infrastructure increased from $879,582 to $1,027,053. The average cost due to disruption of normal operations increased from $955,429 to $1,207,965.
So, What’s Changed?
Security was a modest part of the services you’ve provided—until now. It’s made its way to the forefront of business IT needs so you can protect against the top cybersecurity threats out there. Endpoint protection, firewall protection, and email protection were staples of the managed services business, but they’re simply not enough anymore. Failure to address these increases the chance of a serious security event, and reduces the chance to avoid downtime, a work stoppage, or worse.
For years, MSPs have provided a successful security strategy that has provided their customers excellent uptime and productivity. Cybercriminals are getting more sophisticated and targeting small to medium businesses. Ransomware, data breaches, and phishing attacks are examples of tactics that eclipse the solutions that we’ve relied on thus far. You’ll want to make sure they’re safeguarded against these more sophisticated attacks, and mitigate as much risk as possible. Cyber issues today don’t just impact your customers, but their customers, suppliers, etc. If someone were to breach your customer, it could give them access to all of their critical systems and data. If an incident happens in a regulated industry, the cause goes beyond their loss of business. It would compromise your patient’s protected data and be in breach of HIPAA requirements. Aside from financial implications due to a work stoppage, breaches in industries that are regulated (financial, healthcare, industrial, government, etc.) are also subject to investigations, digital forensics teams, and litigation.
As an MSP, more times than not you’ll be questioned and have to participate in those investigations. If the customer has cyber insurance, the insurance company will do their investigation before paying out. In a breach today where data is compromised, the financial impact is a whopping $148 per record. It’s not just downtime that can render a business in trouble after a breach, because the lingering effects are crippling to most companies.
What Can You Do About It?
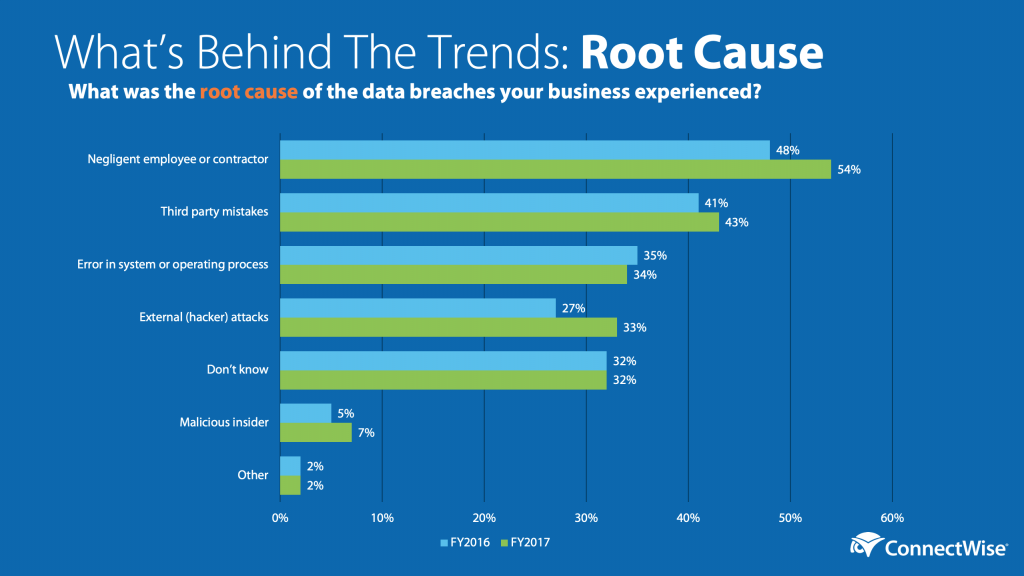
Several things. First, realize that this is not a problem you can throw a bunch of tools at to fix. People and process is a key component of a strong security posture. As you can see in the chart “What’s Behind the Trends: Root Cause”, 54% of data breaches were a result of negligent employees or contractors. That correlates to nearly half of all attacks being executed through phishing or social engineering. Implementing security awareness training through Customer Security Programs is a good way to expand your service offering and reduce your customers risk that doesn’t involve adding another tool to your stack.
Second, leverage a proven framework as a benchmark to measure your customers’ businesses (and your own). We believe the NIST Cybersecurity Framework (CSF) is the most comprehensive and easiest framework for MSPs to adopt. We’ve built a risk assessment based on that framework that includes strengths and weaknesses for your customer, plus an actionable report and an attestation letter that protects you against recommendations your customer doesn’t wish to add. With this, you can walk into a customer’s office and say, “In order to make sure you’re as protected as you can be, I went ahead and did a risk assessment of your business to help determine your security posture. The assessment is based on the Cybersecurity Framework created by the National Institute of Standards and Technology, and it’s the benchmark we use to grade all companies—regardless of size or industry. It’s also the same assessment I perform regularly on my own company.”
This article was provided by our service partner : connectwise.com

