How Mobile Device Management Can Reduce Mobile Security Risks
Today’s modern workplace is home to users who carry their work and personal lives in their pockets. From smartphones to tablets, mobile devices keep us connected and always working. Users can work from anywhere, but that means opening the door to security threats if mobile devices aren’t properly protected. Mobile Device Management is service that help provide that protection.
The Bad News
Mobile security risks are real, and they are expanding every day. Public Wi-Fi networks open the door to hackers who can take advantage of security holes and access confidential company information stored on mobile devices. If a mobile device becomes infected with malware, the malware could spread through the entire network.
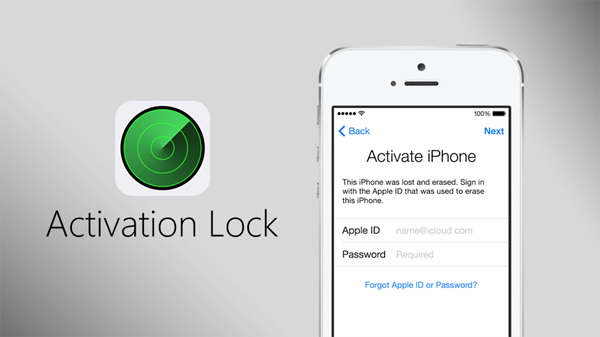
The portability of mobile devices means a greater risk for loss and theft. When unprotected devices disappear, they put access to sensitive business information in unauthorized hands. No business wants to worry about the repercussions of outside access to proprietary information. Just picture the headlines: CEO’s Lost iPhone Leads to Customer Data Breach.
The Good News
Mobile device management (MDM) solutions can help protect against the threats that are out there. Mobile Device Management helps you make sure critical information is protected no matter how your clients’ employees access it.
MDM gives you the ability to enforce minimum security requirements on mobile devices that access your client networks, which helps protect against data compromise. Lost devices can be found with geo-location tracking. If they don’t turn up, the devices can be remotely wiped to protect data with a just a few mouse clicks. Security settings can be adapted to require passcodes, set a time before auto-lock, auto-wipe devices after a maximum number of failed login attempts, and more.
The point is, MDM keeps your clients’ networks better protected. The extra layer of data security gives your clients peace of mind and helps you maintain your role as a trusted advisor. With that in mind, what do you need to look for in an MDM solution?
If you really want to get the most from your MDM solution, look for one that’s going to work easily with your existing solutions. Integration with your remote monitoring and management (RMM) platform and other automation solutions will save you time in setup and implementation, and will enable your technicians to manage mobile devices through the same interface through which they’re already managing your clients’ computers.
In short, the right MDM solution means you’ll be better able to protect vital data from mobile security risks while keeping your clients’ users connected to the information they need to do their jobs.
Now you know what MDM can do to keep your clients safe from mobile threats. Check back next week for tips to help you explain the benefits of Mobile Device Management to your clients and make the sale.
This article was provided by our service partner Labtech.