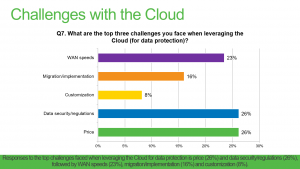
Many CIOs are now adopting a cloud-first strategy and backing up and recovering critical data in the cloud is on the rise. If you don’t have a permanent CIO to manage your IT department, consider hiring an interim CIO. As more and more companies explore the idea of migrating applications and data to the cloud, questions like “How secure are cloud services?” arise. While there isn’t a standout number one concern when it comes to cloud computing, the one thing we can be sure about is that security is front and center in CIO’s minds. Veeam has identified the top two concerns from our recent 2016 customer survey to be security and price. See the graph of responses below:
Quite inevitably, cloud has come with new challenges and we’ll be exploring them all in this cloud challenges blog series. It has also come with some genuine security risks but as we will uncover, cloud backup security has more to do with your implementation of it to successfully ensure data security when moving to the cloud. With cloud, security has to be top priority. The benefits of flexibility and scalability you get from the cloud should not mean sacrificing any security at all.
What are the most important cloud backup security risks?
Stolen authentication/credentials
Attacks on data happen more often than not due to weak password usage, or poor key and certificate management. Issues tend to happen as multiple allocations and permission levels begin to circulate and this is where good credential management systems and practices can really help.
One-time generated passwords, phone-based authentication and other multifactor authentication systems make it difficult for attackers wanting to gain access to protected data because they need more than just one credential in order to log in.
Data breaches
Data breaches can be disastrous for organizations. Not only have they violated the trust of their customers by allowing data to be leaked, but it also opens them up to facing fines, lawsuits and even criminal indictments. The brand tarnishing and loss of business from such an event can leave a business with a long road to recovery at best.
Despite the fact that cloud service providers typically do offer security methods to protect tenants’ environments, ultimately you – the IT professional – are responsible for protection of your organization’s data. In order to protect even the idea of a breach, you need to become a fan of encryption. If you use cloud for storage, experts agree data should be encrypted at no less than 256-bit AES (Advanced Encryption Standard) before it leaves your network. The data should be encrypted a second time while in transit to the cloud and a third time while at rest stored in the cloud. It is important to do your research and enquire into the encryption used by the application, and by the service provider when the data is at rest in order to ensure safe and secure cloud backups.
Lack of due diligence
A key reason moving data to the cloud fails, becomes vulnerable or worse becomes subject to an attack or loss is due to poor planning and implementation. To successfully implement a cloud backup or disaster recovery strategy, careful and deliberate planning should take place. This should first involve considering and understanding all of the risks, vulnerabilities and potential threats that exist. Secondly, an understanding of what countermeasures need to be taken in order to ensure secure restore or recovery of backups and replication, such as ensuring your network is secure or access to key infrastructure is restricted. Due diligence in approaching the cloud should also involve an alignment of your IT staff, the service provider and the technologies and environment being leveraged. The service provider must be seamlessly integrated with the cloud backup and recovery software you plan to utilize for optimal security and performance of your virtualized environment.
Multi-tenant environment
Service providers offer cost-effectiveness and operations efficiencies by providing their customers with the option of shared resources. In choosing a service that is shared, it’s essential that the risks are understood. Ensuring that each tenant is completely isolated from other tenant environments is key to a multi-tenant platform. Multi-tenant platforms should have segregated networks, only allow privileged access and have multiple layers of security in the compute and networking stacks.
Service provider trust and reliability
The idea of moving data offsite into a multi-tenant environment where a third party manages the infrastructure can give even the boldest IT professionals some anxiety. This comes with the perceived lack of control they might have on cloud backup security. To combat this, it is essential to choose a service provider you trust who is able to ease any security doubts. There are a variety of compliance standards a provider can obtain, such as ISO9001 or SOC 2 & SSAE 16 and it’s important to take note of these as you search for a provider. In addition to standards, look for a service provider that has a proven track record of reliability – there are plenty of online tools that report on provider network uptime. Physical control of the virtual environment is also paramount. You must seek a secure data center, ideally with on-site 24/7 security and mantraps with multi-layered access authentication.
So, is the cloud secure?
Yes, the cloud is secure but only as secure as you make it. From the planning and the processes in place, to the underlying technology and capabilities of your cloud backup and recovery service. All these elements combined can determine your success. It is up to you to work with your choice of service provider to ensure the security of your data when moving to cloud backups or DRaaS. Another critical aspect is partnering with a data management company experienced in securely shifting and storing protected data in the cloud.
Veeam and security
We provide flexibility in how, when and where you secure your data for maximum security matched with performance. With AES 256-bit encryption, you have the ability to secure your data at all times: During a backup, before it leaves your network perimeter, during movement between components (e.g., proxy to repository traffic), for when data must stay unencrypted at the target and while your backup data is at rest in its final destination (e.g., disc, tape or cloud). It is also perfect for sending encrypted backups off site using Backup Copy jobs with WAN Acceleration.
You have a choice over when and where you encrypt backups. For example, you can leave local Veeam backups unencrypted for faster backup and restore performance, but encrypt backups that are copied to an offsite target, tape or the cloud. You can also protect different backups with different passwords, while actual encryption keys are generated randomly within each session for added backup encryption security.
Here are some links with more details on encryption and related information:
This article was provided by our service partner Veeam