Recovering Disabled Apple Devices
The Evolution of Mobile Security
Information Security is a major priority in today’s mobile driven world. While devices like your phone are meant to be as accessible as possible, the contents are meant to remain private. Apple, a mobile industry leader, is always developing better solutions to keep your information safe. However, for every step Apple takes to keep up with new threats, their consumers are responsible for taking equal measures. The stakes have never been higher as the cost of securing your device also means potentially losing all device functionality!
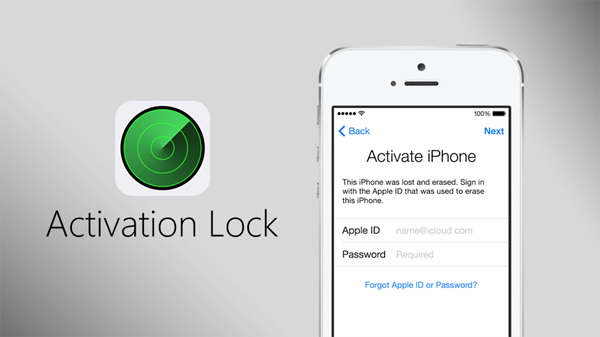
It was only a few years ago our devices were only locked away behind a simple 4-digit passcode. If the passcode were ever lost, one would simply need to wipe the device and set it up as new. While this was effective in protecting our data, it was not effective in protecting our devices themselves. Apple wanted to take security a step forward and dissuade mobile theft entirely. Apple began implementing an online activation lock. Now even if an iPad, iPhone, or Mac were wiped, they would continue to remain locked until the original owner signed in to their Apple account and unlocked the device.
Getting Caught in the Net
While Apple’s activation lock proved very successful in combating black-market resale of mobile devices, it also caused headaches for registered owners. Many users found that misplacing a password meant that their devices were held hostage by Apple. Businesses would need to maintain even tighter control over their inventory in order to prevent accidental lock-outs. This could mean overhauling their entire internal process, something that wouldn’t simply happen over-night. While Apple’s security policies did far more good than harm, some mistakes were bound to happen. Luckily there are a few things we can do to get our devices back under control!
Regaining Control of your Mobile Device
If your device is asking you to enter an Apple ID and Password for an account that you don’t recognize, you will need to contact Apple in order to verify ownership.
- Contact Apple and provide a purchase receipt
- Contact Apple and provide the device serial # and answer purchase related questions
Contact Apple by phone, chat, or through an Apple Store: http://www.apple.com/contact/
Preventing the Problem with Mac OSX Server
Don’t fret! There is light at the end of the tunnel. Apple provides businesses with a few tools to manage and maintain their own devices, including the ability to control Activation Lock! By leveraging Apple’s Business Device Enrollment Program and Mac OSX Server software your business can have full control over its mobile devices. No need to call Apple to unlock your own phone again.
- Apple’s Business Device Enrollment Program (DEP) was designed to shift control of Apple’s mobile security to the business owners. This allows IT to maintain large environments with a single administrator, rather than having users responsible for their own devices. Once a device is enrolled, your business maintains complete control over the configurations, profiles, and security; no middle man. The best feature is allowing users to add personal accounts to the devices without interfering with the business configuration. Users can be given usage rights to a device, rather than becoming temporary owners.
- Mac OSX Server has mobile device management (MDM) tools built in that allow an administrator to make changes and tweak all devices owned by the business. Rather than making adjustments like adding WiFi hotspots or configuring email one device at a time, profiles can be implemented for individuals, divisions, or the entire company.